Water infrastructure facing new security threats
Water infrastructure, including pumping stations, treatment plants, reservoirs, and distribution networks, plays a critical role in the functioning of modern societies.
These facilities ensure the supply of drinking water, wastewater treatment, and the management of water resources. Their continuous operation is therefore essential for both communities and economic activity.
Today, these infrastructures face increasing risks:
- intrusions at remote facilities
- equipment sabotage
- manipulation of sensitive installations
- attempted contamination
- disruption of water distribution networks
In this context, physical access security has become an essential component of infrastructure protection.
Access control represents a first line of defense for limiting risks and securing critical installations.

Distributed infrastructure that is difficult to secure
Unlike many industrial environments, water infrastructure is often spread across large territories.
Operators must secure numerous sites such as:
- pumping stations
- water capture points
- reservoirs
- treatment facilities
- technical installations
This geographic dispersion makes monitoring more complex and increases the importance of reliable centralized access management.
Modern access control systems allow operators to manage multiple sites from a single interface while maintaining strong local protection.

Managing access in an operational environment
Water infrastructure involves many different stakeholders:
- operations teams
- maintenance technicians
- engineering companies
- external contractors
Access rights must therefore be carefully managed to:
- quickly grant access permissions
- limit access to necessary areas
- revoke rights immediately after interventions
- maintain traceability of site access
An effective access control system allows organizations to combine strong security with operational efficiency.

Access traceability: a key element for incident management
Within critical infrastructure, knowing who accessed which facility and when is essential.
Access traceability helps to:
- quickly identify the origin of incidents
- strengthen the protection of sensitive installations
- improve operational oversight
- support security audits
Access control therefore becomes a valuable operational management tool.

Water infrastructure and cybersecurity: anticipating NIS2 requirements
Water infrastructure is now recognized as essential to societal functioning.
As a result, it is included in the sectors impacted by European cybersecurity regulations such as the NIS2 Directive.
Operators must therefore strengthen their risk management strategies by integrating:
- physical site security
- cybersecurity measures
- protection of industrial systems (IT/OT)
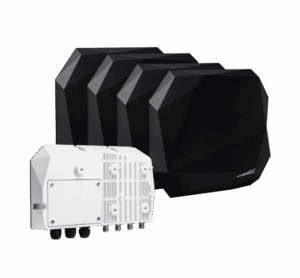
Modern access control systems must be capable of integrating seamlessly with existing architectures while aligning with recognized security frameworks such as:
- NIS2 Directive
- ISO 27001
- IEC/EN 62443 for industrial cybersecurity

Access control: a strategic tool for securing water infrastructure
Today, access control goes far beyond simply opening doors.
It has become a strategic tool to:
- secure critical installations
- manage access for employees and contractors
- ensure traceability of interventions
- strengthen overall infrastructure security
With open and interoperable technologies, water operators can improve security while maintaining simple and scalable management.
At STid, we design solutions adapted to the real challenges of critical infrastructure: site protection, access management, and seamless integration into industrial environments.
Discover our taylor made solutions for the energy business
Explore solutions specifically developed to support your day-to-day operational and security needs


Need help? Contact us
Still looking for product information? Start by consulting our FAQ.
Still no answer? Don’t hesitate to contact us